LastPass Gives Small Businesses Encrypted Vaults, Passwordless Sign‑In, and SaaS Visibility with Business Max
LastPass centralizes password management for small businesses with encrypted vaults, passwordless sign‑in, and Business Max tools for SaaS and AI monitoring.
Why routine security hygiene matters for small teams
Everyday security habits—the ways employees create, store, and share credentials, which AI tools they adopt, and how quickly administrators can detect and respond to risky access—are core determinants of organizational safety. The pressure to keep digital operations simple often clashes with the need for strong protections: employees balk at complex logins, and lean IT teams must balance usability against limited resources. The result is a persistent gap: small and midsize organizations face a disproportionate share of incidents that originate in human error, and they need solutions that reduce risk without turning security into a full‑time job.
LastPass positions itself as a tool to address that gap. Presented as a password manager aimed at business use, LastPass offers encrypted personal vaults for employees and administrative controls that are intended to centralize credential governance, reduce attack surface as a company’s digital footprint grows, and provide signal into employee security behavior.
How LastPass organizes credentials and admin controls
At the core of the product offering is the separation between individual user vaults and centralized administrative visibility. Employees receive encrypted vaults where they can store, share, and manage passwords. According to the vendor description, those vaults are encrypted locally under a zero‑knowledge model, meaning the encrypted data remains on the user’s device and cannot be read or intercepted by LastPass itself.
For administrators, LastPass provides tools for policy enforcement and oversight. The administrative side is described as enabling real‑time audits, policy enforcement, and visibility into the workforce’s security posture so IT teams can detect weak, reused, expired, or breached credentials and alert users. This combination is intended to let organizations apply controls centrally while keeping everyday password management convenient for individual employees.
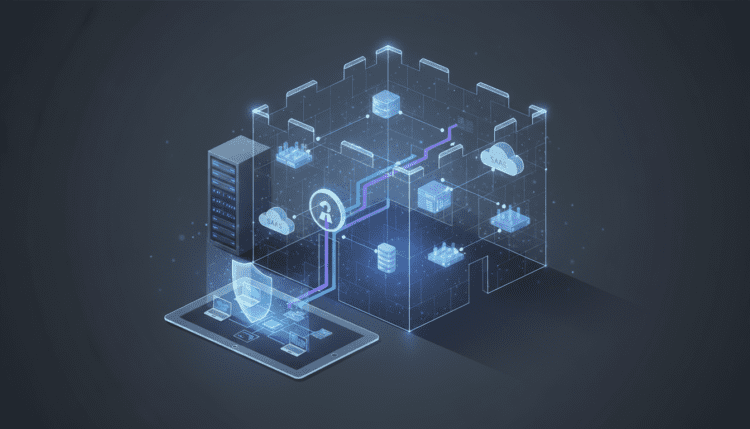
Tracking unmanaged SaaS and AI with Business Max
Unmanaged SaaS and externally adopted AI services are called out as a particular source of risk when they operate outside an organization’s technology stack. The LastPass Business Max plan is described as giving IT administrators the ability to monitor every SaaS application and login employees use from a centralized dashboard. That visibility is paired with controls to block or restrict access when a threat is observed.
The platform’s administrative workflow is presented as supporting immediate action: when an administrator identifies a weak, reused, expired, or breached credential, they can alert the affected user and guide them to safer options; when a worker uses an unauthorized or high‑risk AI or SaaS tool, security teams can refine usage policies to restrict or block that tool. Those capabilities are framed as a way for lean IT teams to respond quickly to emerging threats without adding excessive operational overhead.
Zero‑knowledge encryption, extension deployment, and passwordless options
LastPass’s security model is presented as zero‑knowledge: encrypted vault data is kept on the user’s device and is not accessible in plaintext to LastPass. The vendor cites this model as a core privacy and security characteristic of how vaults are handled.
Deployment is described as achievable through a browser extension, which the vendor says avoids the need for additional agents or proxies to manage credentials. That delivery model is positioned as complementary to existing and future enterprise stacks, allowing organizations to adopt credential management without installing further endpoint agents.
On authentication options, LastPass reports support for passwordless authentication methods intended to reduce breaches that stem from stolen credentials. The platform includes biometric‑powered passkeys and FIDO2 hardware key support as alternatives to traditional password sign‑in. These options are presented as ways to move away from shared or reused passwords toward cryptographic sign‑in methods.
Practical capabilities: what LastPass does, how it works, and why it matters
What it does: LastPass provides encrypted personal vaults for employees, centralized policy and visibility for administrators, monitoring of SaaS and AI usage under Business Max, and support for passwordless sign‑in methods.
How it works: User credentials and vault entries are encrypted locally in a zero‑knowledge model so data remains on the user’s device in encrypted form. The product can be deployed via a browser extension, and administrators interact with a centralized dashboard to audit activity, enforce policies, and take corrective action when insecure behaviors are detected.
Why it matters: The vendor frames LastPass as a way to reduce attack surface and human‑error risk across credential and SaaS usage. By combining user‑facing convenience—encrypted vaults and simplified sign‑in—with administrator controls for audits and policy enforcement, the product aims to make routine security hygiene achievable for teams with limited IT resources.
Who can use it: The messaging is targeted at small and midsize businesses and lean IT teams that need to balance security controls with usability for employees. The Business Max plan is positioned as the tier that adds visibility and control over SaaS and AI application use.
When it’s available and how to try it: The vendor invites organizations to start a free trial or schedule a live demo, and promotional messaging indicates a time‑limited offer of 30% off any LastPass plan for new customers.
Operational workflows for administrators and employees
For administrators, the platform centers on visibility and response. The dashboard described in vendor materials surfaces SaaS apps and logins used by employees, flags credential problems such as reuse or breach, and enables blocking or restriction of risky applications. That creates a workflow where an administrator can pivot rapidly from detection (for example, a flagged credential or an unauthorized AI tool) to remediation (notifying the user, enforcing a policy, or blocking access).
For employees, the goal is reduced friction. Personal encrypted vaults give individuals a place to store and share passwords and credentials without requiring administrators to manage each secret directly. Passwordless options—biometric passkeys and FIDO2 hardware keys—are positioned as alternatives for users who prefer not to manage complex passwords while also reducing exposure to stolen credentials.
Integration and fit with existing security stacks
LastPass is described as deployable through a browser extension, which the vendor highlights as a way to avoid installing additional agents or proxies on endpoints. That delivery approach is presented as intentionally non‑intrusive so organizations can adopt credential management without heavy changes to endpoint configurations or infrastructure.
By design, the product claims to complement existing enterprise technologies rather than replace them, offering a credential governance layer that sits alongside current authentication, identity, and device controls. The platform’s policy and auditing features are framed to work in concert with broader security practices rather than requiring a wholesale shift in tooling.
Implications for developers, security teams, and business leaders
The product positioning raises several implications for different stakeholders. For developers and IT teams, a centrally administered password manager with passwordless support can simplify credential handling in environments where shared or hard‑coded secrets are a problem. For security teams, the ability to monitor SaaS and AI adoption provides a signal into shadow IT and emergent threats, enabling faster policy updates and targeted remediation.
For business leaders, the vendor argues that a balance of usability and control reduces friction for employees while giving administrators the oversight needed to lower human‑error risk. The reported upward trend in vulnerabilities—cited in the vendor’s 2025 cybersecurity trends material as an annual growth of more than 20%—is presented as a contextual driver for adopting tools that aim to future‑proof organizations against an expanding threat surface.
Use cases and business scenarios where LastPass is positioned to help
The vendor messaging highlights a few common scenarios for small and midsize companies: replacing password fatigue with practical protections, managing an expanding inventory of SaaS applications and AI tools, and shifting toward passwordless sign‑in to limit credential theft. The combination of employee vaults and administrative controls is shown as a fit for organizations that need to enforce policies and conduct audits without dedicating significant engineering resources to credential administration.
Common business workflows outlined include alerting users to compromised or weak credentials and guiding them to safer alternatives, and blocking or restricting unauthorized SaaS or AI usage when it is detected through administrative monitoring. Those are presented as mechanisms for reducing exposure and responding to incidents driven by human actions or shadow IT adoption.
Limitations and boundaries described by the vendor
The presentation focuses narrowly on credential management, SaaS visibility, and passwordless options. It emphasizes the zero‑knowledge encryption model, local encryption of vault data, and extension‑based deployment. The materials do not describe bespoke integrations, specific architectural diagrams, or independent benchmark results; they do not claim elimination of all risk, nor do they provide a comprehensive threat model within the promotional text.
Getting started: trials, demos, and promotional offers
The vendor invites prospective customers to try LastPass through a free trial or by scheduling a live demonstration. Promotional messaging in the source material also notes that new customers can receive a 30% discount on any LastPass plan. The Business Max plan is singled out as the edition that adds SaaS and AI monitoring and centralized ability to block or restrict access from the dashboard.
Broader industry context and developer considerations
Credential hygiene and shadow IT visibility are recurring themes in enterprise security conversations. The vendor cites a trend where the volume of new vulnerabilities is growing—reported as over 20% per year in the referenced 2025 trends material—underscoring why organizations prioritize tools that can scale with their attack surface. For developers and product teams, the availability of passwordless authentication (biometric passkeys and FIDO2 hardware keys) aligns with industry movement toward stronger, phishing‑resistant authentication methods.
Security and developer tooling ecosystems—identity providers, single sign‑on solutions, endpoint management, and automation platforms—are frequently mentioned in the industry as adjacent areas where credential and access management matter. While the LastPass messaging positions its browser extension and zero‑knowledge vaults as complementary to existing stacks, teams planning an adoption should evaluate interoperability with identity providers, provisioning workflows, and automation pipelines as part of any deployment.
Operational considerations for adoption
Adopting a centralized credential manager implies changes to user workflows and administrative processes. The vendor suggests that LastPass reduces friction for users through encrypted vaults and passwordless options, while giving administrators auditing and enforcement capabilities. Organizations should consider how notification workflows will operate when credentials are flagged, how policy changes will be communicated to employees, and how SaaS usage data from the dashboard will be incorporated into existing security operations.
Because the platform’s deployment model includes a browser extension, IT teams will want to verify extension compatibility across the browsers and environments their users rely on and plan for extension rollout and updates. The vendor emphasizes that no additional agents or proxies are required for credential management, which could simplify rollout in environments where installing endpoint software is burdensome.
A realistic adoption plan will align product capabilities—encrypted vaults, administrative audits, Business Max SaaS monitoring, and passwordless support—with internal policies, incident response playbooks, and user training to ensure the expected behavioral changes take root.
A forward look at how credential and SaaS controls influence business risk
Credential management and SaaS governance remain foundational elements of an organization’s security posture. Tools that combine user convenience—encrypted vaults and passwordless sign‑in—with administrative visibility over SaaS and AI usage are being positioned as a practical response to growing vulnerability volume and the rise of shadow IT. For small and midsize organizations that lack large security teams, the appeal lies in reducing human‑error exposure while enabling faster, policy‑driven responses to risky activity.
As threat landscapes evolve and organizations adopt more cloud and AI tools, the interplay between credential hygiene, passwordless authentication, and centralized SaaS visibility will continue to shape procurement and operational decisions. The combination of a zero‑knowledge encryption model, extension‑based deployment, and administrative controls is one approach vendors are offering to help businesses keep pace without overwhelming limited IT resources. Future developments are likely to emphasize stronger integration with identity and access management ecosystems, broader support for passwordless standards, and continued refinement of SaaS discovery and policy enforcement to meet changing operational needs.