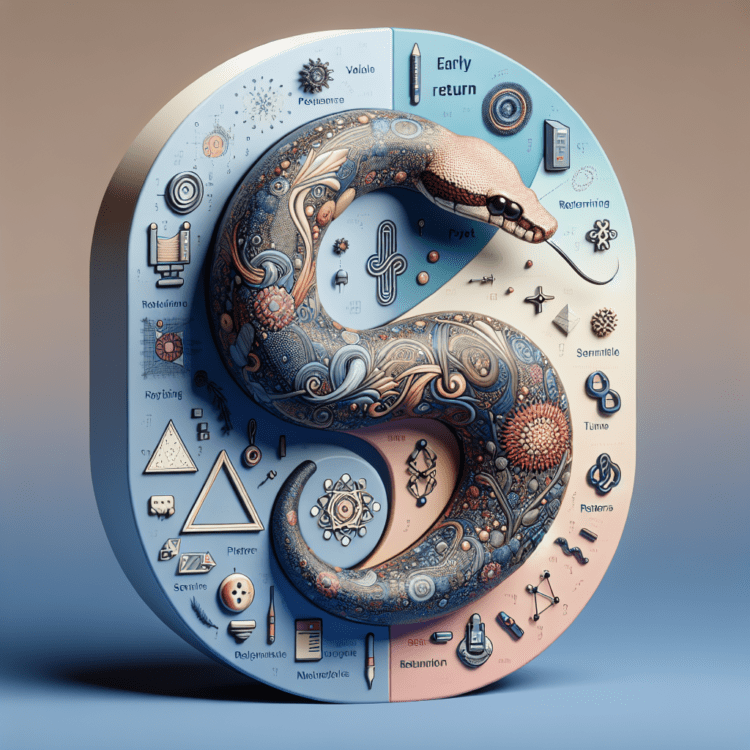
Pydantic and the early return pattern: how guard clauses and rule-as-data validation keep Python checks flat and readable
Pydantic and the early return pattern: using guard clauses and rule-as-data validation to flatten logic, fail fast on bad input, and simplify data checks.
The moment validation logic starts growing, nested if/else chains tend to take over. This article examines a compact approach that blends the early return (guard clause) pattern with simple, data-driven rules — and shows how that combination produces validation code that is easier to read, change, and extend. The discussion references Pydantic as a schema validation tool for ensuring correct data shape and types, and positions early return as a lightweight strategy for handling edge cases immediately rather than entangling the main logic in deep nesting.
Why nested validation becomes hard to maintain
When a validation task begins, checks are often few and straightforward: confirm a numeric field meets a minimum, verify a string contains an expected character, ensure an identifier is the right type. As new checks are added, each condition often nests further inside prior ones, producing a pyramid of indentation. That structure still works functionally, but it quickly becomes difficult to scan, challenging to modify, and error-prone when new rules must be injected into the sequence. The nested approach effectively mixes "what" you want to validate with "how" you traverse the checks, and the result is brittle code that discourages change.
What the early return (guard clause) pattern means for validation
In procedural terms, a return sends a value back from a function and immediately halts the function’s execution. The early return or guard clause pattern uses that behavior intentionally: for each precondition or invalid state, the function exits early with an error result. That transforms validation from a ladder of nested conditions into a series of short, local checks. Each guard is a checkpoint: if the condition fails, return an explanatory result; otherwise continue. The pattern places error handling up front so the primary path remains flat and focused on the successful case.
Defining rules as data instead of hardcoded branches
Rather than encoding each validation step as an if statement buried in logic, the pattern replaces condition code with a compact set of rule descriptors held in simple data structures. Each rule identifies:
- the target field,
- the kind of check (for example: type check, minimum value, substring containment),
- a reference value for the check (for example: an expected type, a numeric minimum, or a substring).
Because rules are plain data, they are easy to read, to add to, or to serialize. New validations can be appended to the list of rules without editing the core validation loop. This separation—rules as declarative data, validation function as the executor—moves the code closer to describing "what" to validate rather than encoding a procedure of nested tests.
How a single rule-driven validator operates
A compact validator iterates the set of rule descriptors and applies each to the corresponding field in the input record. For each rule the function:
- checks whether the required field exists and returns an immediate error if it does not;
- retrieves the field value and performs the type, minimum, or containment check specified by the rule;
- returns early with a structured failure when a rule does not pass;
- proceeds to the next rule when the current rule succeeds.
If the loop completes without triggering a guard return, the function returns a success result. The early-return style ensures failures are reported at the first relevant point and that the success path remains unobstructed by nested control flow.
How this pattern behaves on a representative record
Consider a record that contains a user identifier, an age, and an email value. If a ruleset requires user_id to be an integer, age to meet a minimum threshold, and email to include an at-sign, the validator checks each rule in order. If the age is below the threshold, the validator returns a failure object indicating which field failed and why. Because the function returns as soon as a rule fails, later rules are not evaluated for that input; the response describes the immediate obstruction to proceeding.
Readable outputs and predictable flow
The validator returns structured results that make downstream handling straightforward: a failure response includes status, the field in question, and a short issue description; a success response communicates readiness to proceed. That predictable, single-format response simplifies automated reporting, logging, or translation of failures into a table when running the validator across datasets.
Why flat logic improves maintainability
Flat logic produced by early returns has several practical benefits:
- It is easier to scan for intent: each rule is a small, self-contained assertion rather than part of an indented block.
- The core validation function is reusable and rarely needs modification when adding or changing rules.
- Teams can version or configure rule sets independently from the code that enforces them, enabling configuration-driven validation.
- Error messages are localized to the rule that failed, reducing the cognitive load of tracing which condition produced a failure.
When to use this pattern versus schema-based tools
The article’s source contrasts the rule-driven, early-return approach with schema validation provided by libraries such as Pydantic. Pydantic is called out as an effective schema validation solution for ensuring incoming data has the expected shape, types, and formats. The early return pattern is presented as a complementary technique: while schema libraries enforce structure and types at the boundary, guard clauses handle edge cases and invalid states immediately within application logic, keeping flow control simple and explicit. The two approaches address overlapping concerns but operate at different levels—schemas for structural guarantees, guard clauses for immediate failure handling and straightforward logic flow.
Developer ergonomics and extensibility
Because rules are data, adding a new validation is often as simple as appending another rule descriptor. The validator’s implementation does not need to change for every new check; it only needs to support the set of rule types the application requires. That reduces the risk of bugs from change and lowers the friction for evolving validation requirements. Teams can also store rules in configuration files or a database and reload them without editing validation code, which helps decouple validation policy from code deployment cycles.
Common rule types and how they map to real checks
A small set of rule kinds covers many use cases encountered in basic input validation:
- type checks: confirm the value is an instance of an expected type (for example, integer);
- minimum checks: enforce numeric lower bounds (for example, age must be at least 18);
- contains checks: ensure strings include required substrings (for example, an email must contain ‘@’).
These rule categories can be expressed uniformly in the rule data structure and interpreted by a central validator, which makes the strategy predictable and easy to document for other developers.
Practical considerations when adopting the pattern
There are a few practical points to bear in mind:
- Rule ordering matters when the validator returns at the first failure. Place the most critical checks earlier if you want to catch them first.
- The validator must decide how to represent failures in a way that client code can consume; a small, consistent response shape is helpful.
- For complex validation logic—cross-field checks, pattern matching, or transformations—rule descriptors may need to be extended or the validator supplemented with specialized functions. The pattern scales best for independent, field-level assertions.
- When running validation across datasets, converting results into a table for analysis is a natural next step; the source suggests that outputting aggregated results encourages inspection and reporting.
How the approach fits into data validation ecosystems
This pattern is lightweight and deliberately minimal. It resembles the smallest elements of larger validation solutions but focuses on clarity rather than feature richness. In contexts where a full schema library is preferred for broad guarantees or advanced parsing, these guard-style checks still have a role for preconditions and early failure pathways. The article frames the rule-driven, early-return validator as a useful complement to schema validation tools, not necessarily a replacement for them.
Security and robustness considerations
By returning early on missing or malformed fields, guard clauses reduce the chance that later logic will operate on unexpected data. That immediate rejection simplifies reasoning about what the rest of the code can safely assume. However, for security-critical inputs or complex normalization needs, relying solely on simple rule descriptors may be insufficient; such scenarios typically call for more comprehensive schema validation and sanitization tactics. The pattern helps keep the codebase tidy and defensive, but it should be integrated into a broader set of validation and safety practices where necessary.
Developer workflow and collaboration benefits
Because rules are easy to scan and update, the approach supports collaboration between engineers and non-engineers who influence validation policy. A rules-as-data model can be reviewed, stored in version control, and modified without changing the validator’s internal structure. That lowers the friction for iterative policy updates and makes it simpler to automate tests that exercise each rule case. The separation of concerns—policy declared as data, enforcement encoded once—encourages cleaner code reviews and clearer ownership of validation policy.
How the pattern can be extended
The central validator can be extended to support additional rule kinds as needs evolve. Examples of safe extensions suggested by the pattern include adding pattern checks for string formats, integrating custom type validators for domain types, or enabling optional fields. Each new check type can be introduced as a new rule descriptor and handled in the validator’s existing loop, preserving the flat structure and early-return behavior. The source also suggests that turning validator results into tabular output for dataset-wide runs is a straightforward enhancement that fits the pattern’s semantics.
Broader implications for teams and systems
Adopting a guard-clause, rule-driven validation style can influence how teams think about data quality. It encourages a declarative mindset—specify the expectations, externalize them as data, and rely on a small enforcement engine. That shift promotes clearer communication about validation requirements, lowers the cognitive cost of small changes, and reduces the chance that subtle control-flow bugs will hide in deeply nested conditionals. For organizations that already use schema tools like Pydantic, the pattern complements existing practices by handling immediate checks and edge-case early exits in application logic.
When this pattern is most effective
The pattern is particularly well suited to codebases that:
- perform many small, independent field-level checks,
- need to keep the validation flow readable and easy to update,
- prefer to express validation rules in configuration-like structures,
- and want explicit, localized failure reporting.
It is also useful as a quick, pragmatic approach for prototyping validation behavior before investing in a larger schema or policy system.
This lightweight rule-driven approach puts the focus on describing validation intent and treating errors as first-class, early-return responses. By flattening control flow and isolating checks into a simple loop that evaluates data-driven rules, developers get clearer code and more predictable outputs. The combination sits naturally alongside schema validation libraries such as Pydantic — where Pydantic provides structural guarantees, and guard-clause validation captures immediate, application-specific edge cases — offering a pragmatic path to cleaner, more maintainable data handling.
Looking ahead, this pattern can be refined into richer validation pipelines: rule metadata could be extended to include severity levels, suggested fixes, or localization keys for error messages; validators could be configured to collect multiple failures rather than returning on the first one; and rule sets might be versioned and managed alongside feature flags to let teams evolve validation policy safely. Whatever direction is chosen, the core idea remains practical and portable: express what must be true about data as readable rules, and use early returns to keep validation logic flat and focused.